North Korea’s internal computer operating system includes spying tools capable of tracking documents offline, the first in-depth analysis has revealed.
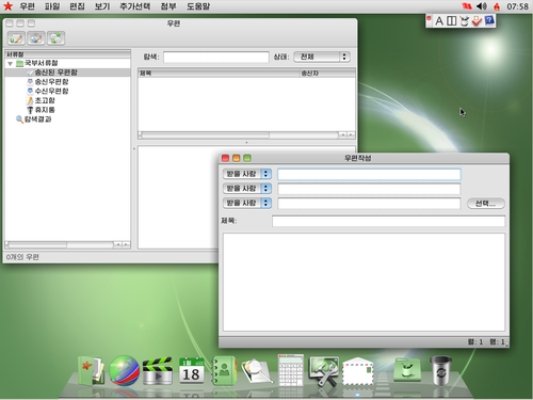
Red Star OS was designed to superficially mimic Apple’s OS X, but hidden features allow it to watermark files and tie them to an individual.
The tools were discovered by two German researchers who conducted the analysis over the past month.
The presented their findings at the Chaos Communication Congress on December 27.
Florian Grunow and Niklaus Schiess pored over the code of Red Star OS version 3.0, which first surfaced online about a year ago.
Any files uploaded to computer via a USB stick or other storage device can be watermarked by the system, allowing the state to trace the journey of that file from machine to machine. Red Star can also identify undesirable files and delete them without permission.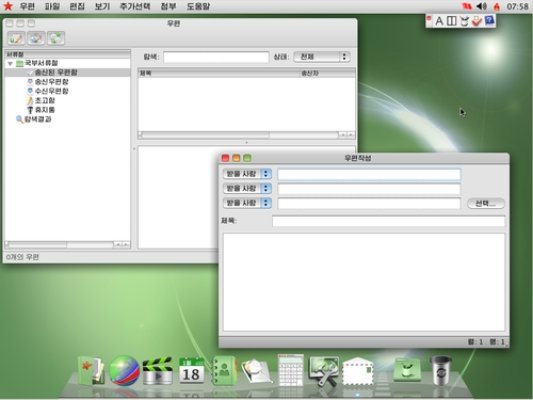
The watermarking function was designed in response to the proliferation of foreign films and music being shared offline.
The system will imprint files with its individual serial number, although it is not known how easily the state can link those serial numbers to individual users.
One element puzzling Florian Grunow is the discovery of an extended version of the watermarking software which he and Niklaus Schiess do not fully understand, but which he says may help identify individual users.
Red Star also makes it nearly impossible for users to modify the system. Attempts to disable its antivirus software or internet firewall will prompt the system to reboot.
The idea for an internal operating system was first conceived by Kim Jong-il, according to Florian Grunow.
As with many things about the world’s most insular state, the extent to which Red Star is used in North Korea is not known. It is likely installed in libraries and other public buildings, says Florian Grunow, where operating systems are installed by the state.
Red Star was built using Linux, a free and open-source platform which can be modified at will, and was designed that way to make it as accessible as possible.
More ironic still is the name of the file used by Red Star to hunt for suspicious files on the machine.
https://www.youtube.com/watch?v=KTBemKiSgWI